Vulnerability Management
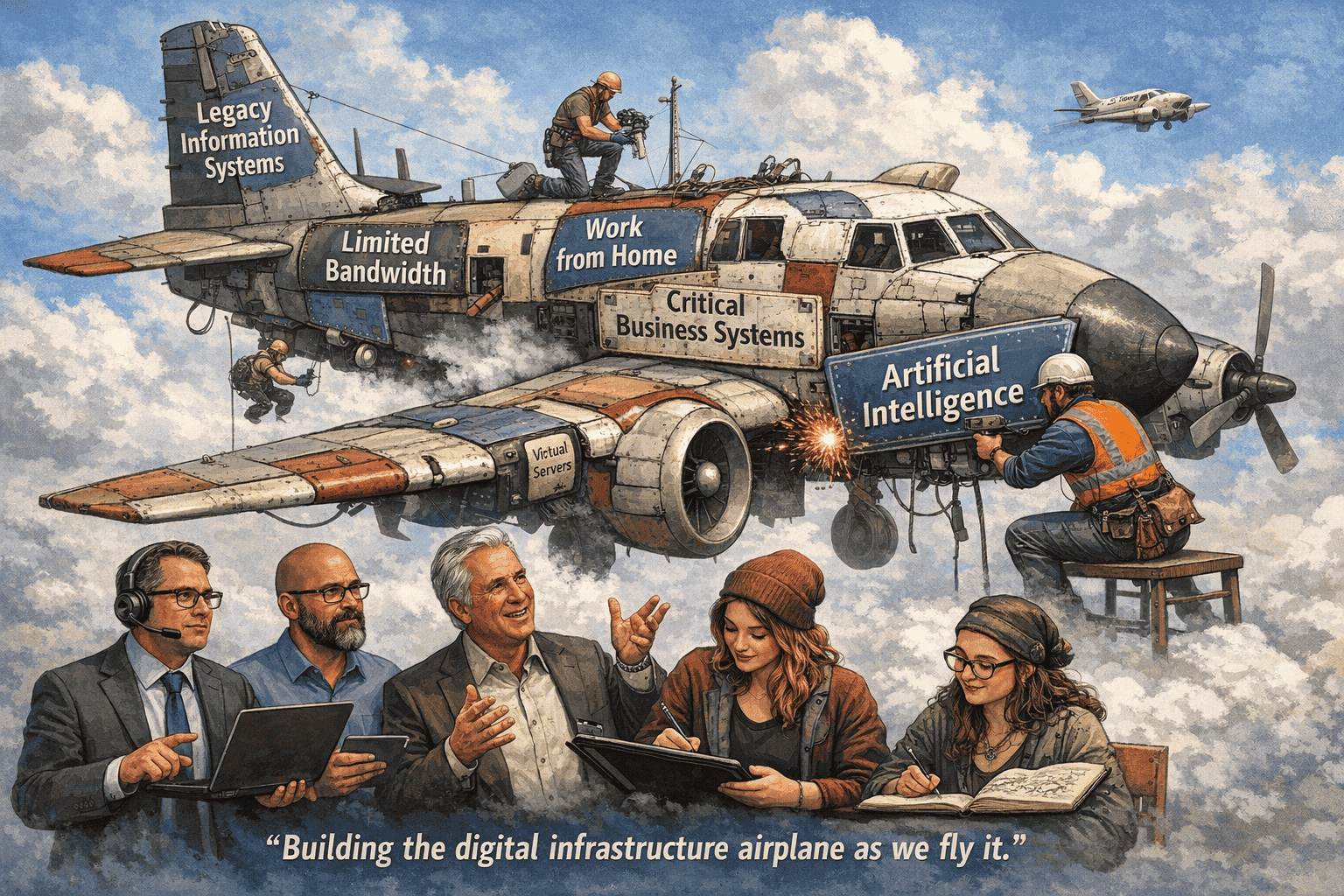
2026 Vulnerability Management is becoming increasingly complex as organizations face visibility gaps, resource shortages, and rapidly evolving cyber threats. As digital environments expand across cloud, on-premise, and hybrid infrastructures, maintaining a consistent and effective vulnerability management strategy is no longer a simple operational task—it is a critical business function.
In this white paper, Pearl Technology’s cybersecurity professionals—Anthony Mini, Peter Beaugard, Stephen Harayda, Yvonne Murphy, and Mike Strickler—examine the growing challenges associated with enterprise vulnerability management in 2026. Their analysis highlights the risks organizations face when vulnerability management is treated as a routine process rather than a strategic initiative. Effective programs require coordination across teams, deep technical expertise, and a risk-based approach to prioritization and remediation.
The authors emphasize that many of today’s most significant cyber incidents stem from failures in basic security hygiene. Industry data shows that approximately 60% of breaches are tied to known vulnerabilities that had available patches but were never applied. High-profile incidents such as Equifax, WannaCry, and Log4Shell demonstrate how delays in patching and poor visibility can result in widespread compromise, financial loss, and long-term reputational damage.
The paper explores several core challenges, including a shortage of skilled personnel and the difficulty of translating vulnerability scan data into actionable remediation steps. It also highlights persistent issues with asset inventory and visibility, noting that many organizations lack a complete, real-time understanding of their environments—leaving critical systems unscanned and exposed.
Another key theme is prioritization. Traditional vulnerability scoring systems often fail to account for real-world business context, making it difficult for organizations to focus on what truly matters. Risk-based vulnerability management is presented as a more effective approach, enabling teams to reduce exposure by prioritizing vulnerabilities most likely to be exploited.
Additional challenges include compliance-driven security practices, network segmentation limitations, and inefficient workflows between security and IT teams that delay remediation. The paper also addresses the accelerating speed of exploitation, with attackers leveraging automation and AI to weaponize vulnerabilities within days—or even hours—of disclosure.
Ultimately, the white paper positions vulnerability management as a foundational but often underestimated pillar of cybersecurity. Organizations that adopt a proactive, integrated, and risk-focused approach will be better positioned to reduce risk, strengthen resilience, and avoid becoming the next high-profile breach.
To read the white paper… Download it now! Does your business need help with IT solutions, cybersecurity, data centers, or audiovisual integration? Contact us to see what technology solutions might work best for you. We are excited to partner with Rapid 7! https://www.rapid7.com/