IT Infrastructure Projects, Delivered and Operated by Pearl
End-to-end execution across network, cloud, communications, and data center, engineered for performance, scalability, and long-term reliability.
Strategic IT Projects, Engineered for Growth
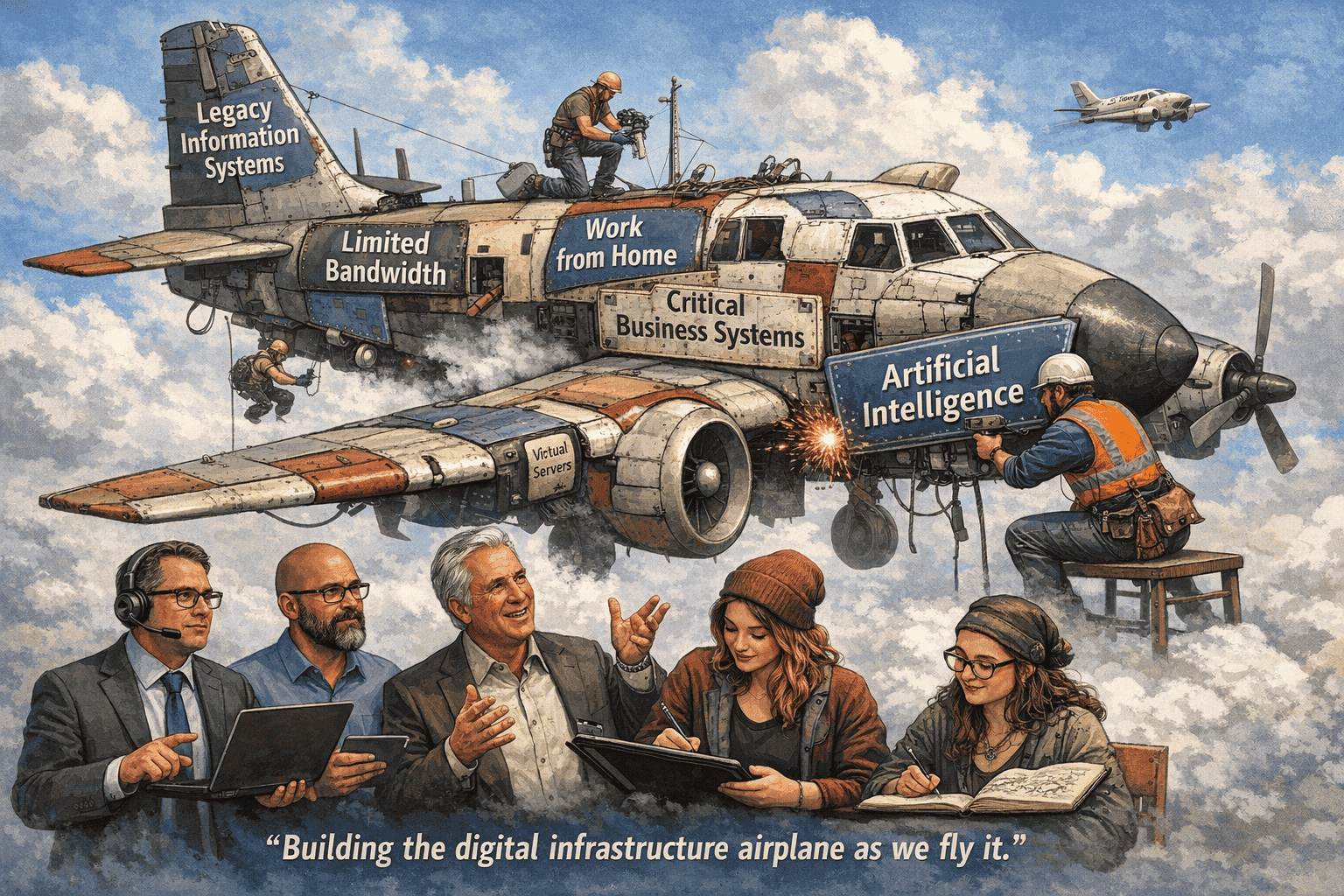
Pearl Technology delivers end-to-end IT project execution designed to modernize infrastructure, eliminate operational friction, and align technology with business performance. We architect integrated environments where network, cloud, communications, and data center systems operate as a unified platform, not as disconnected tools. From high-performance network infrastructure and enterprise wireless to next-generation firewall architecture, we build resilient foundations that support demanding workloads and distributed teams. This is tightly integrated with public and private cloud environments, enabling seamless workload mobility, predictable performance, and controlled cost structures across hybrid architectures.
Beyond deployment, Pearl designs and operates technology environments for long-term efficiency, scalability, and continuity. We optimize cloud and private cloud platforms to improve utilization and visibility while avoiding unnecessary complexity. Communication systems, including VoIP, secure email, threat protection, and continuity, are engineered to keep operations running without interruption. At the core, our data center and infrastructure strategies are built for availability and rapid recovery, leveraging virtualization, enterprise storage, and redundant design to ensure your business remains operational, adaptable, and prepared for disruption.
Network Infrastructure
- Cisco Systems Routing and Switching
- Palo Alto Networks Next-Generation Firewalls
- Aruba Enterprise Wireless LAN Solutions
- Cisco Meraki Solutions
Data Center
- Private & Public Cloud
- HPE and Cisco UCS Servers
- Nimble Storage SAN Solutions
Cloud: Private, Public, Hybrid
- Microsoft Azure
- Amazon Web Services
- Pearl Data Center Hosted Virtual Servers
Communications Solutions
- Microsoft Office 365
- Barracuda
- Spam Filter and Advanced Threat Prevention
- Cloud Archiving
- Email Continuity
- Impersonation Protection
- Email Encryption
Proactive IT Operations That Keep Your Business Running
Pearl Technology delivers proactive IT operations designed to prevent disruption, not just respond to it. We continuously monitor and manage your environment to identify and address issues before they impact performance, uptime, or user productivity. When action is required, our engineering team responds quickly, on-site or remotely, with the depth of expertise needed to resolve issues at the root, not just the symptom.
Execution is driven by structured project management and clear communication at every stage. We provide consistent weekly updates, defined milestones, and direct access to escalation paths when needed, ensuring nothing stalls or falls through the cracks. Built on ITIL-aligned practices, our approach brings discipline to service delivery while keeping IT aligned with evolving business priorities, so your technology remains stable, predictable, and capable of supporting growth.
Read Current News From Our Team
Working in today’s cyber landscape requires a variety of changing technologies. Get ideas from our team, so you can more readily evolve to meet your organization’s needs.
Replatforming Virtual Infrastructure: Navigating Cost and Compliance Challenges
Future Proof Submitted by: Anthony Mini, President & Rob Judd, Director Data Center Operations The way organizations consume infrastructure is undergoing a structural shift—not just in technology but in financial strategy as well. What was once a straightforward CapEx decision

Pearl Technology Named to the Prestigious CRN Tech Elite 250 List for 2026
Pearl Technology has been recognized by CRN, a brand of The Channel Company, on its 2026 Tech Elite 250 list.

2026: Vulnerability Management: Pain Points and Trends
Vulnerability Management 2026 Vulnerability Management is becoming increasingly complex as organizations face visibility gaps, resource shortages, and rapidly evolving cyber threats. As digital environments expand across cloud, on-premise, and hybrid infrastructures, maintaining a consistent and effective vulnerability management strategy is