SOC Services
Among the tools we use for your organization’s defense-in-depth strategy is our Security Operations Center (SOC services), which includes all the services it provides. This means we can provide your business with continuous monitoring and defense, a SIEM platform, and immediate incident response to help keep your organization from experiencing expensive and reputation-damaging cyberattacks.
SOC Services:
Security Information & Event Management (SIEM)
Collect, normalize, and aggregate log data to deliver efficient data access and management. Our SOC services SIEM platform utilizes real-time monitoring to observe activity at the exact moment it occurs within your network environment. It also aids in incident investigation to search and drill down on logs to further investigate a potential incident.
SOC Services:
Vulnerability Management
SOC Services:
Security Assessments
Risk Assessment: Information Security Maturity Model to evaluate your information security strategy and receive actionable recommendations on how to improve. Build a comprehensive roadmap to secure your organization. Prioritize changes that increase your organization’s information security the most, with the least effort.
Vulnerability Report: Automated scan looks for known vulnerabilities (unpatched software, misconfiguration, and more) in your assets and generates a report of these vulnerabilities, often highlighting those that represent the greatest risk to your organization.
Penetration Test: Manual and custom approach to demonstrate how vulnerabilities can be exploited, as well as how lateral movement can be utilized to penetrate a network and expose the network and content. By highlighting possible vectors, we reveal the potential costs and much-needed insight.
Cybersecurity Maturity Model Certification (CMMC): We have registered practitioners who are qualified to consult on your implementation of processes and practices associated with the achievement of a cybersecurity maturity level. CMMC is designed to provide increased assurance to the department that a defense industrial base (DIB) company can adequately protect sensitive unclassified information, accounting for information flow down to subcontractors in a multi-tier supply chain.
SOC SERVICES:
Incident Response (IR)
Read Current News From Our Team
Our expert cybersecurity team combines best-in-class technologies with decades of experience to deliver defense-in-depth strategies and custom solutions. Learn how to take a proactive approach to protecting your business.

One Disaster Recovery Tip That Could Save Your Business
Imagine crafting a piece of ransomware, a masterpiece designed to stealthily penetrate defenses, encrypting everything in its path, rendering data inaccessible to its rightful owners. The attack begins with phishing emails, exploiting software vulnerabilities, or brute-forcing weak passwords. Once inside,

Tips to Help Protect Your Data
Given the recent AT&T data breach, Anthony Mini recommends the following:
1. Monitor your accounts with identity protection services.
2. Check the status of your e-mail accounts that have been exposed to other breaches using the website: https://haveibeenpwned.com/.<br
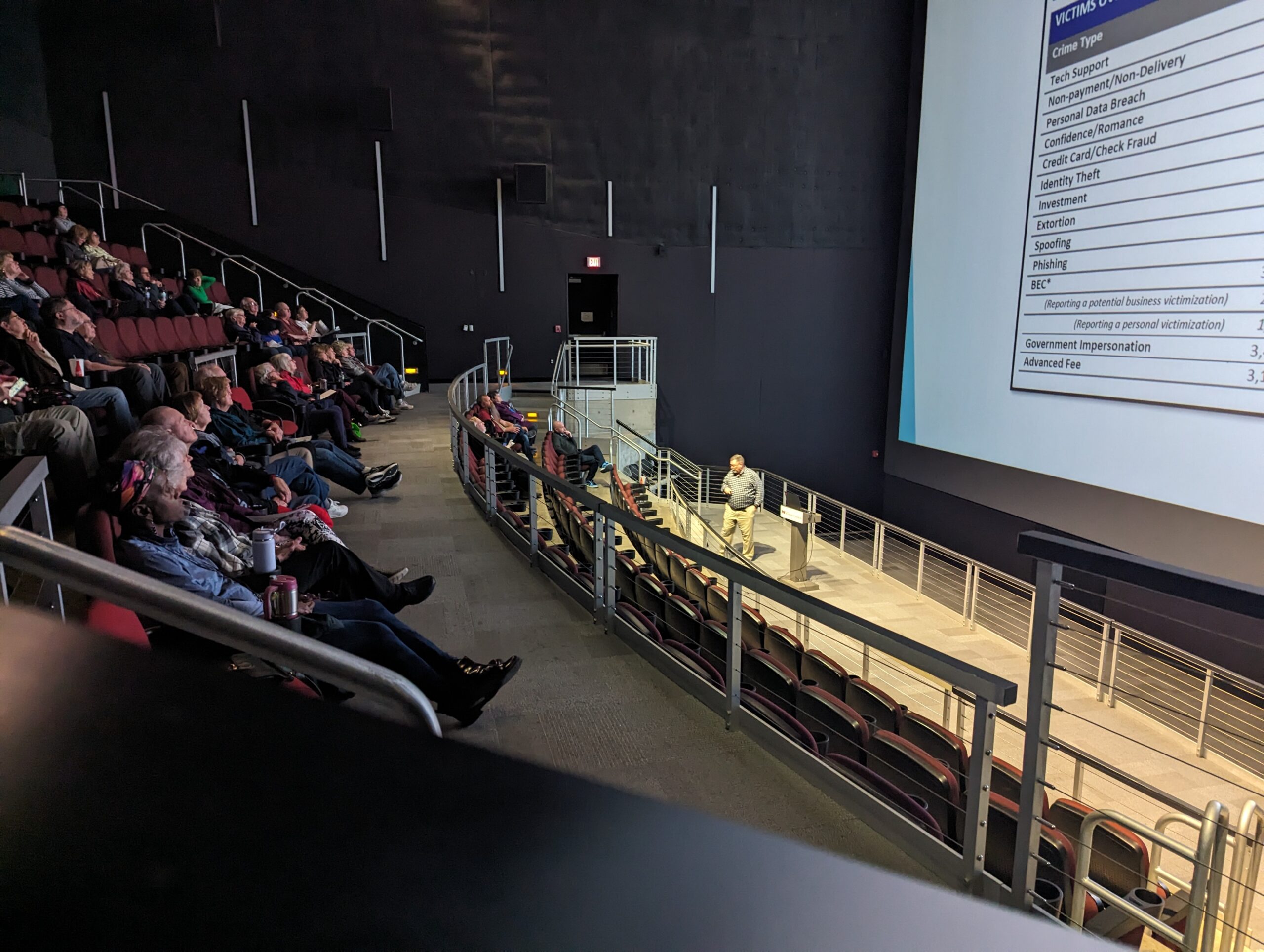
Pearl Technology Hosts Operation Boomerang
Those who attended today’s Operation Boomerang at Peoria’s Riverfront Museum learned some practical tips to stay safe from scammers. The event, which was geared toward protecting seniors from cybercrime, had a great turnout, and attendees walked away with information they