INFORMATION TECHNOLOGY SOLUTIONS—DESIGNED, OPERATED, AND OPTIMIZED BY PEARL
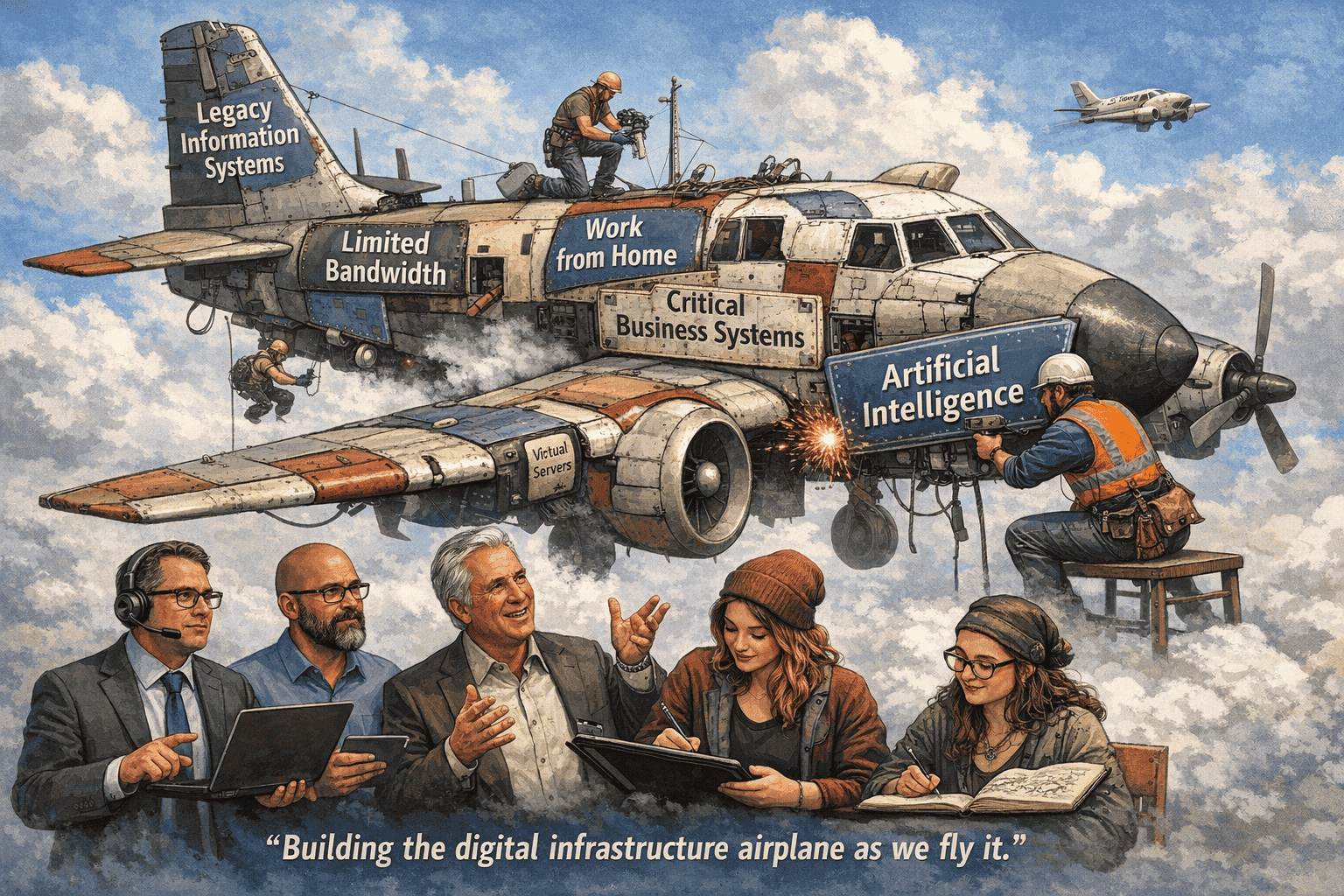
Technology isn’t just a function, it’s the backbone of how your business operates, scales, and competes. Pearl Technology delivers fully integrated IT solutions that span infrastructure, operations, and continuity, combining project execution, managed services, and backup into a single, accountable model. From initial design to ongoing management and continuous optimization, we take ownership of your environment so your team can focus on driving the business forward.
Recognized as a Top MSP 501, named to the CRN MSP 500, and honored with the BBB Torch Award, Pearl brings proven operational discipline and engineering depth to every engagement. With in-house expertise across infrastructure, cloud, security, and data protection, supported by our own data centers and cybersecurity capabilities—we don’t just support technology, we run it. And in a world of AI bots and call trees, Pearl Technology understands the value of real human connection. When you call, you get experienced professionals who know your environment, can make decisions, and are accountable to your success. We operate as a true mission partner—built on trust, responsiveness, and long-term alignment.
INFORMATION TECHNOLOGY SOLUTIONS - Partner
As your full-service IT provider, Pearl Technology delivers customized solutions tailored to your business needs. Our IT consulting and planning services align your technology strategy with your goals. We offer continuous remote monitoring and management, robust email protection, and layered security strategies to safeguard your data. Specializing in Microsoft Office 365, we enhance productivity and collaboration. Our Pearl Backup and Continuity Service ensures your critical data is secure and accessible. Partnering with top industry leaders, we provide the best products and solutions that fit your business requirements and budget. Trust Pearl Technology for excellence in IT solutions.
INFORMATION TECHNOLOGY SOLUTIONS - MonitorinG
Our comprehensive IT solutions ensure your business runs seamlessly by continuously monitoring and detecting potential issues, whether using your equipment or ours. We proactively address IT problems before they occur, providing a robust response to day-to-day situations through our dedicated service desk. Our certified technicians are equipped to resolve issues both remotely and in person, ensuring minimal disruption to your operations. Additionally, we offer a variety of ad hoc solutions tailored to meet your specific needs. Trust our expertise to keep your IT infrastructure secure, efficient, and reliable.
Our Partners
At Pearl Technology, our goal is to simplify technology and make it an asset for your business. As your IT Solutions specialist, we partner with others to help your business with the products and support needed to achieve your goals. These partners help us ensure the most current technology, a seamless process, and a high-quality experience.
Read Current News From Our Team
Working in today’s cyber landscape requires a variety of changing technologies. Get ideas from our team, so you can more readily evolve to meet your organization’s needs.
Replatforming Virtual Infrastructure: Navigating Cost and Compliance Challenges
Future Proof Submitted by: Anthony Mini, President & Rob Judd, Director Data Center Operations The way organizations consume infrastructure is undergoing a structural shift—not just in technology but in financial strategy as well. What was once a straightforward CapEx decision

Pearl Technology Named to the Prestigious CRN Tech Elite 250 List for 2026
Pearl Technology has been recognized by CRN, a brand of The Channel Company, on its 2026 Tech Elite 250 list.

2026: Vulnerability Management: Pain Points and Trends
Vulnerability Management 2026 Vulnerability Management is becoming increasingly complex as organizations face visibility gaps, resource shortages, and rapidly evolving cyber threats. As digital environments expand across cloud, on-premise, and hybrid infrastructures, maintaining a consistent and effective vulnerability management strategy is